This article is cross posted on LinkedIn for comments and discussion.
The vast majority of developers don’t care about security. That’s a fact in my opinion, and it has been the same since I started doing this appsec stuff back in 2000. I say the majority because of course in a massive population of millions of developers, some inevitably do, but almost every developer I have ever talked to, as long as I don’t have a security hat on, has told me that it's not one of their top priorities. Features, bugs, maintaining code, functional testing, performance ….. and yes security is in there somewhere, but it's never a priority if they are being honest. I have run big engineering teams in my career and, shock horror, it wasn't one of my top priorities either. Just being honest. I had to ship features or my boss would get mad. It was implied they would be secure but it was implied and not always expected.
Appsec people have been complaining for years that security should be a priority for all developers, pushing them to take security training and trying to inject security taxes into their workflows. Developer education and awareness is the key and similar phrases are muttered at security conferences everywhere.
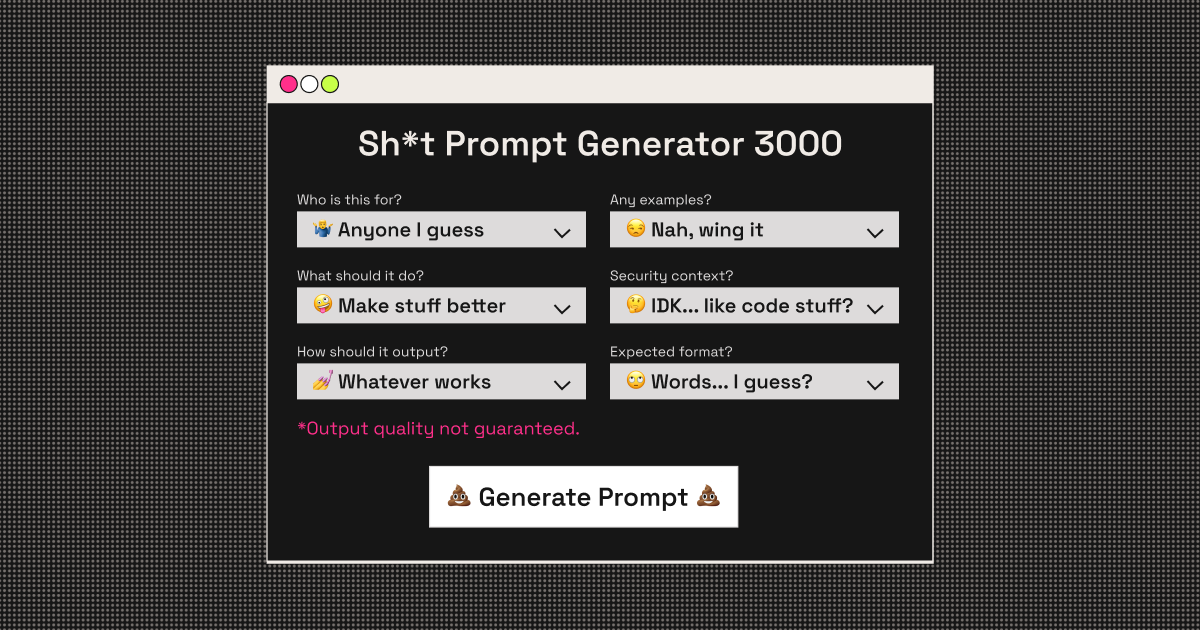
I think people should just get over it and move on, because getting over it and moving on doesn't mean you can’t still enable developers to build secure software, it just means you take a different, less direct approach. No more pushing molasses uphill, no more awkward glances in the office, no more passive-aggressive Slack messages, no more having to make them sit in powerpoint hell, no more staring at useless fucking code review findings filtered from a tool by some intern at an accounting firm playing security consultants on the Internet. Life is too short. YOLO.
Developers are good people. I have only ever met a handful of arsehole developers in my career and most of those were on one team at one company. They were useless twunts as well, which is probably why they were arseholes. Apart from that handful of twunts, my favourite word at the moment, I have found that ALL developers will always do the right thing if
1) it’s easy.
2) it doesn’t get in their way.
3) it doesn’t give them more work.
Better still ALL developers will do the right thing if
4) it solves a problem that they have.
So if you want to improve application security then one of the best and most effective ways in my mind, is to stop trying to make developers care, accept they don't ,and start deploying solutions that solve a problem that they care about that as a side effect improves security or that allows you to tag security on later. Make sure it's easy, doesn't get in their way and make sure it takes work off their plate.
Have a load of crypto issues? Don't try to teach developers crypto, abstract them from having to deal with it. Win win. Authn and AuthZ a PITA. Use Okta. Win Win. Got a vulnerable dependency problem? Deploy Dependabot and get automatic updates sent to the developer as a PR for out-of-date dependencies. Win win.
Mark Mansons book, ‘The subtle art of not giving a fuck’ is on my Audible queue this week. It reminds you to stop fighting ‘the man’ and find happiness in other ways. I think we should accept that developers only pay lip service to security, get over it, and develop security solutions that first and foremost solve a problem that developers have. Then you get to ride the coattails.